Assessment 1 Information
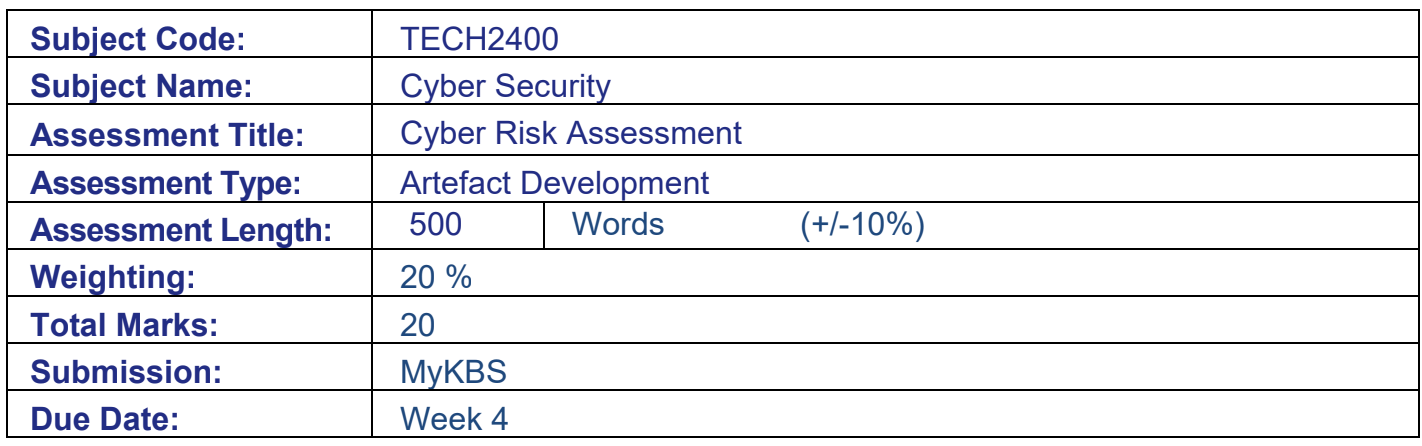
Your Task
Demonstrate your understanding of key cybersecurity concepts aligned with learning outcomes LO1, LO2, and LO3. Identify threats, conduct a risk assessment, and produce a document tailored to non-technical business stakeholders.
Additionally, this task requires you to leverage open-source cybersecurity and generative AI tools, simulating real-world practices in cyber risk assessment.
- LO1: Contextualize the terminology associated with cybersecurity for diverse stakeholders in business.
- LO2: Identify vulnerabilities and threats pertaining to the IT infrastructure of organizations.
- LO3: Recommend risk mitigation strategies to address cybersecurity vulnerabilities and threats.
Assessment Description
This assessment simulates industry practices for conducting risk assessments within a business context. You will demonstrate your ability to investigate network traffic using tools such as nmap and Wireshark and conduct a risk assessment based on the ISO 27001 framework. Additionally, you are expected to utilize generative AI tools, such as ChatGPT or Gemini, to support and enhance your workflow.
Your final deliverable is a comprehensive Risk Assessment Report designed to assist the company's executives in strengthening their cybersecurity posture.
Case Study
Kaplan Care is a small medical practice comprised of several doctors and administrative staff operating in a hybrid work arrangement. The organization's IT infrastructure includes:
- • Patient Records Server: Runs an electronic medical record (EMR) system accessible via HTTP/HTTPS.
- • File Sharing Server: Hosts patient scans and lab reports, shared via the server message block (SMB) protocol.
- • Remote Access Server: Provides virtual private network (VPN) access for remote staff.
Recently, employees of the practice have noticed several anomalies, including:
- • Delayed server responses
- • Unauthorised login attempts on the VPN server
- • Suspicious outbound connections to unrecognised IP addresses
You are provided with two files:
- 1. XML file for Nmap: Pre-generated results simulating a network scan of Kaplan Care’s current infrastructure. Includes details on open ports, running services, and detected vulnerabilities.
- 2. pcap file for Wireshark: Captured network traffic simulating suspicious traffic patterns like plaintext credentials, connections to unusual external IPs, and SMB traffic anomalies. You have been brought in to assess the network’s cybersecurity posture, identify risks, and present recommendations.
Assessment Instructions
1) Identify relevant threats
- a. Use a generative AI tool to help you identify potential cyber risks relevant to Kaplan Care. Include screenshots of your interaction, demonstrating how you have used the tool as a brainstorming assistant and not as the sole source of information.
- b. Review the outputs and select five (5) key risks to include in your report.
- c. List your chosen threats and provide a brief rationale for why each one is significant to the organization.
2) Analyse network traffic
- a. Open your XML file on Nmap and your PCAP file on Wireshark.
- b. Examine the data from both tools to identify any evidence that relates to the risks you previously identified. (e.g., look for anomalies such as unusual ports, IP addresses, or traffic patterns that align with your selected risks).
- c. Document your findings for each of the risks using screenshots of nmap or Wireshark, and provide a brief explanation of the data the supports your findings.
3) Conduct a risk assessment
- a. Use a generative AI tool to help you evaluate the likelihood and impact of each of the five (5) selected threats. Include screenshots of your interaction.
- b. Validate your AI-generated results manually. Identify at least two (2) results that you disagree with, provide alternative assessments, and briefly justify your perspective.
- c. Use the risk matrix below to determine the risk score of each threat.
- d. Considering Kaplan Care’s medium risk appetite, recommend appropriate controls when necessary. Align your recommended controls with industry standards, such as the NIST Cybersecurity Framework (CSF), ISO27001, and the ACSC Essential Eight.
- e. Use a table to present your findings. Your table must include the following columns:
Important Study Information
Academic Integrity and Conduct Policy
KBS values academic integrity. All students must understand the meaning and consequences of cheating, plagiarism, and other academic offenses under the Academic Integrity and Conduct Policy.
Please read the policy to learn the answers to these questions:
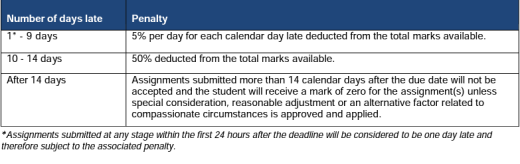
Late submission of assignments (within the Assessment Policy)
Length Limits for Assessments
Penalties may be applied for assessment submissions that exceed prescribed limits.
Study Assistance
Students may seek study assistance from their local Academic Learning Advisor or refer to the resources on the MyKBS Academic Success Centre page. Further details can be accessed at
Submission Requirements
All assessments including draft copies must be written and submitted in English. The use of translation tools is not permitted.
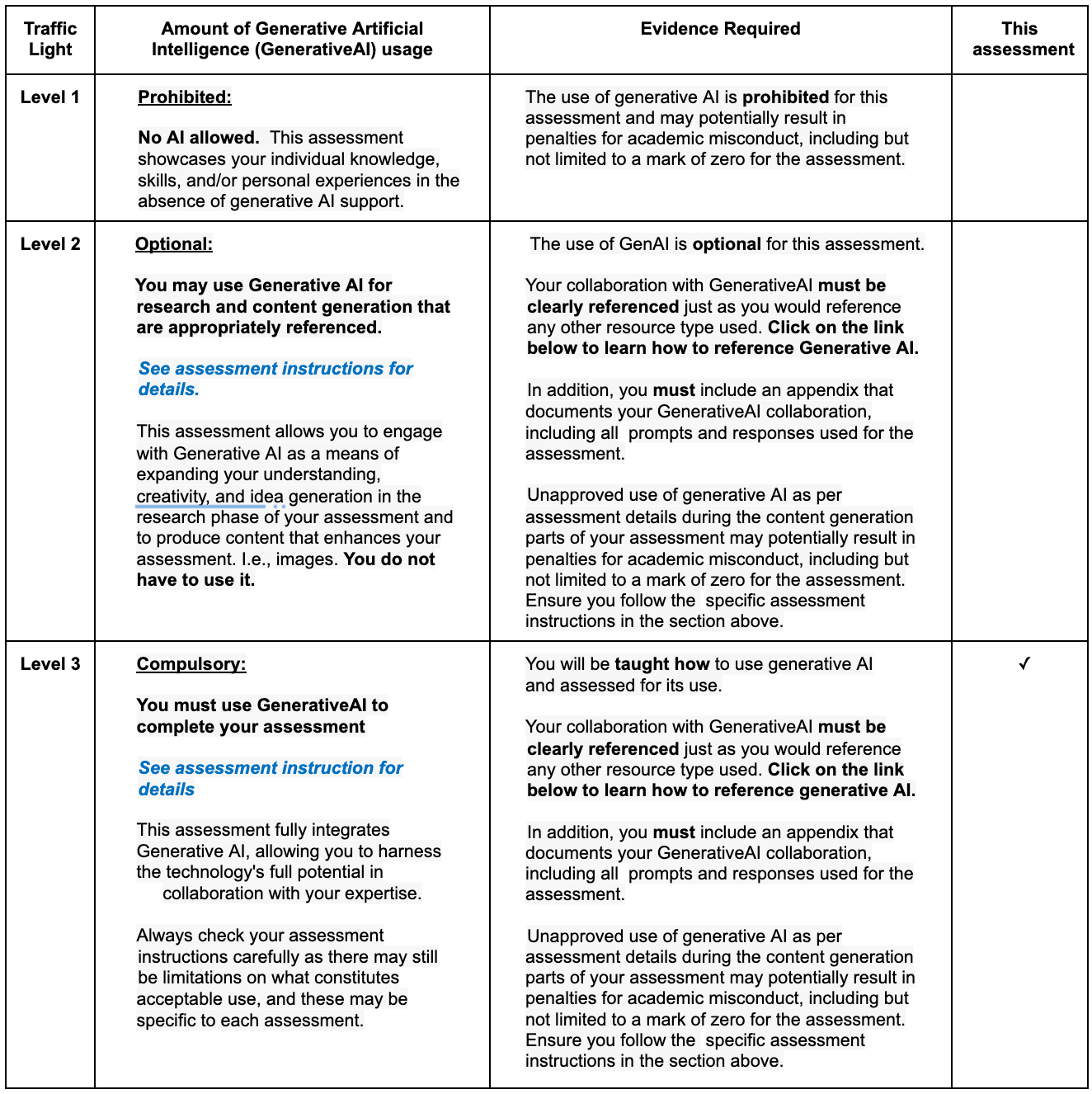
Generative AI Traffic Lights
Please see the level of Generative AI that this assessment has been designed to accept:
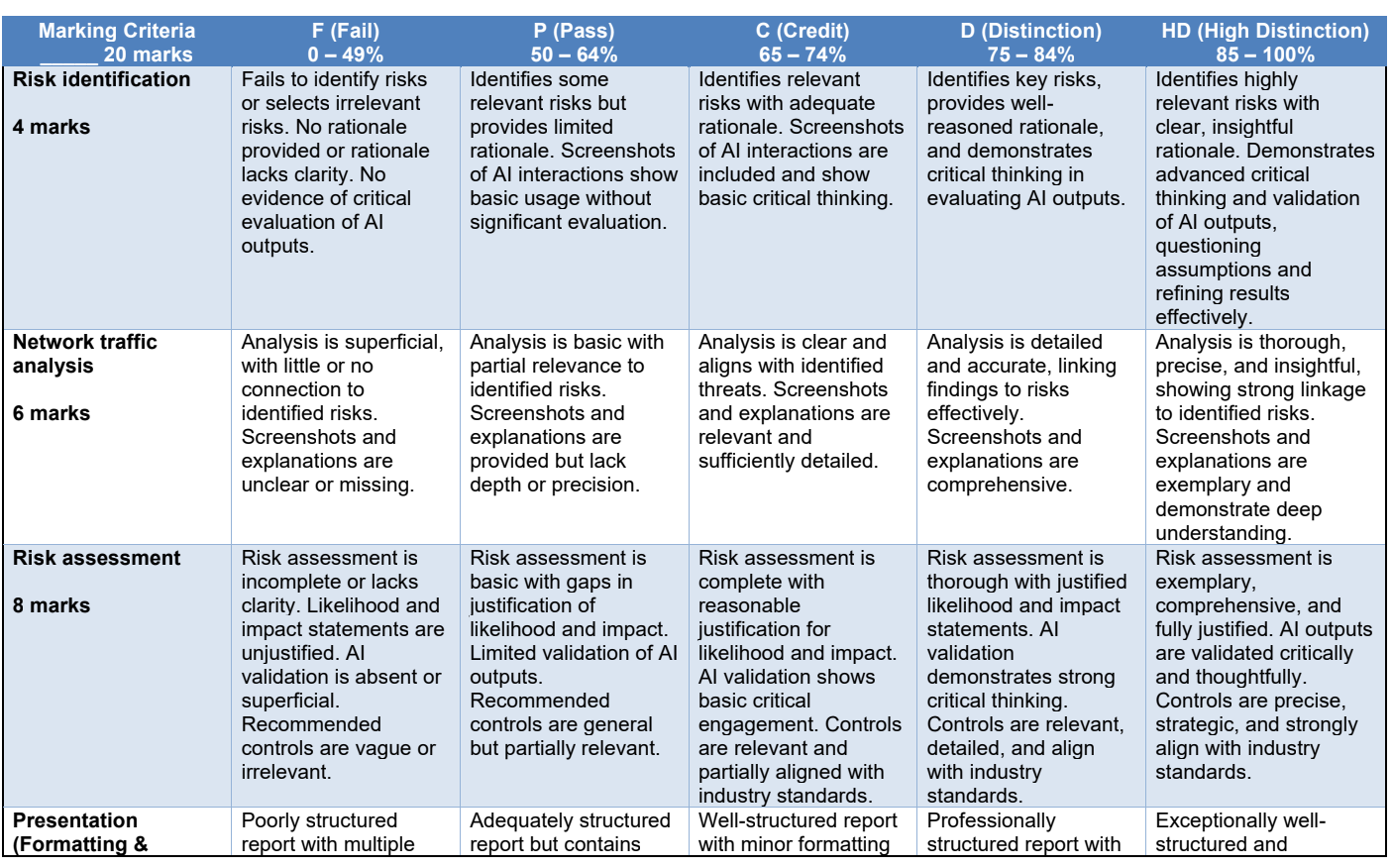
Assessment Marking Guide