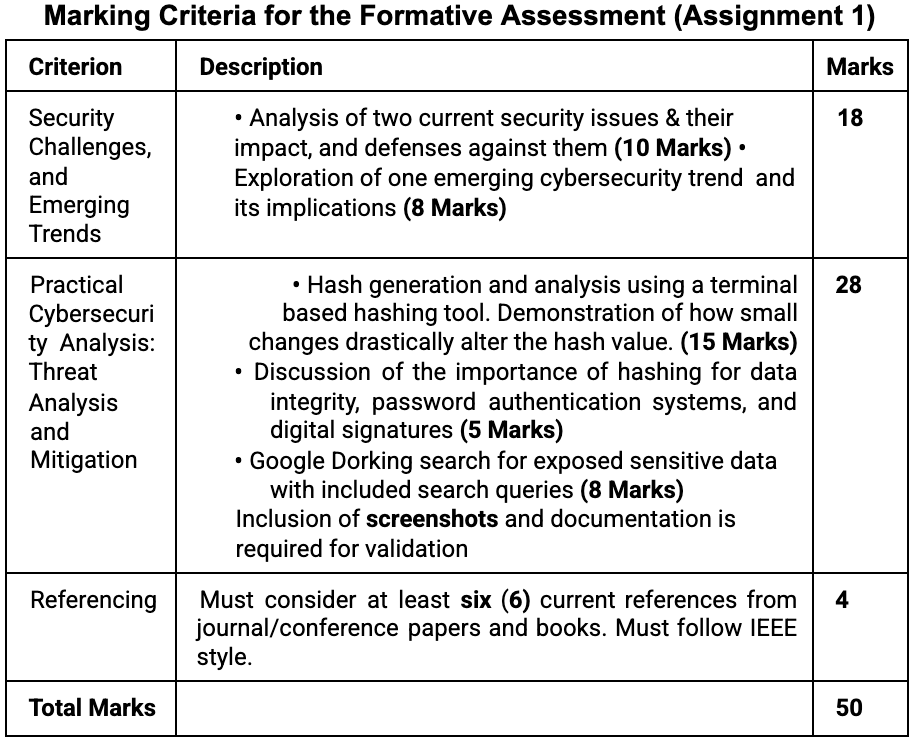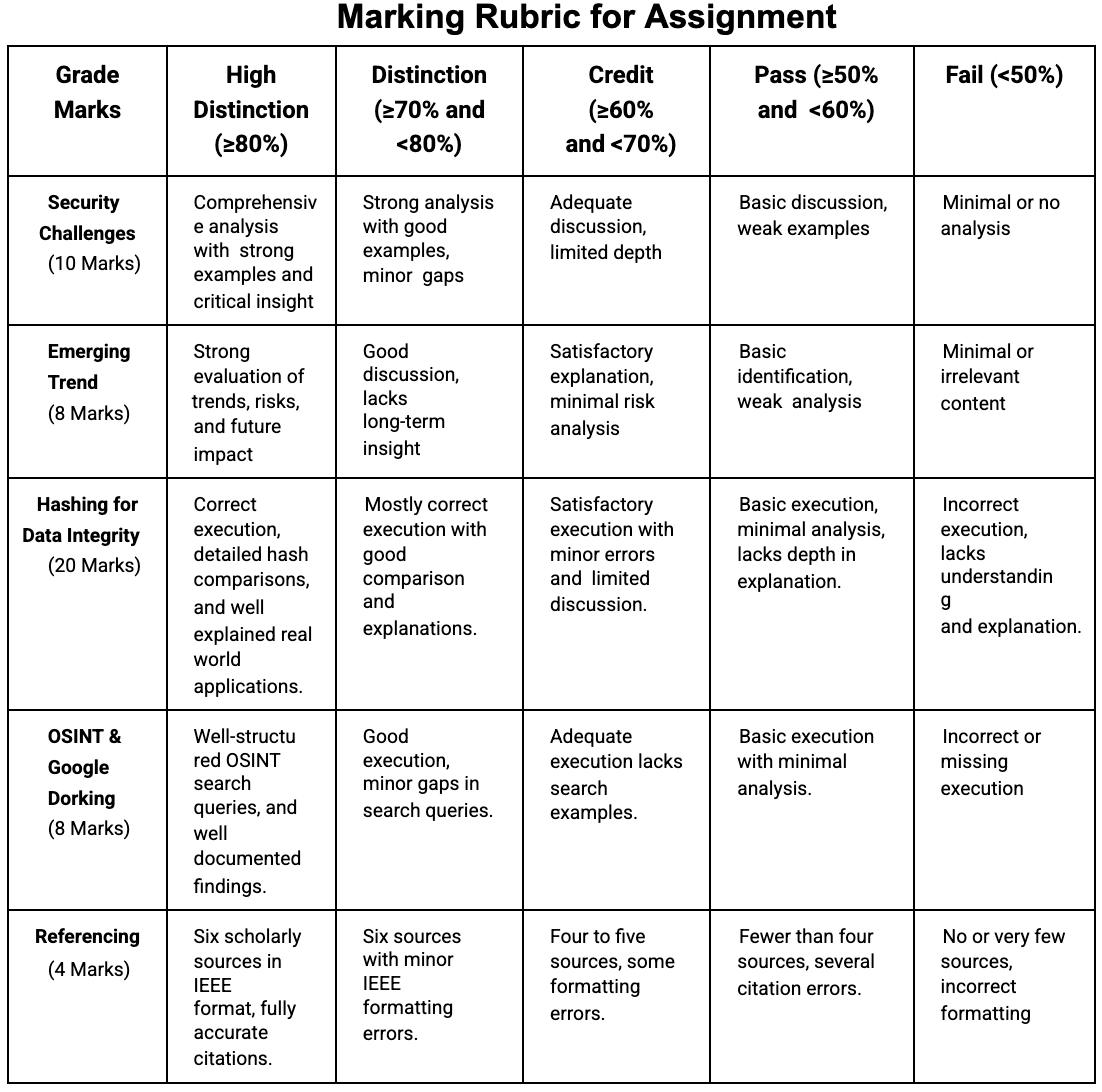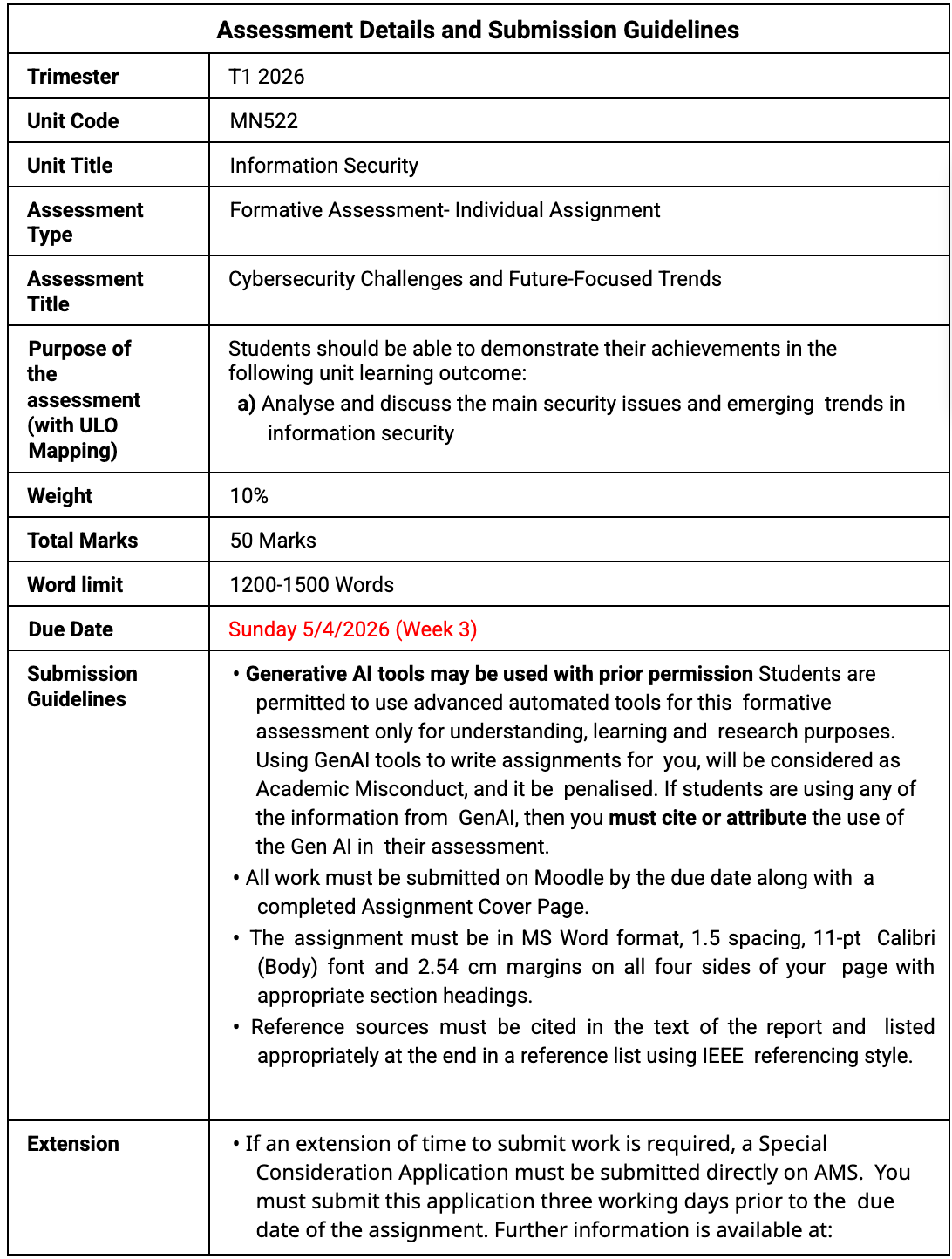
Assessment Overview
This assignment requires students to examine present‑day cybersecurity challenges and evaluate innovative trends shaping the security landscape.
Students must demonstrate analytical thinking, independent research, and practical capability through hands‑on cybersecurity tasks. Screenshots must be included for all technical exercises in Part B.
Part A: Security Challenges, and Emerging Trends
1. Analyse Two Current Cybersecurity Issues (10 Marks)
- • Discuss two major cyber security issues impacting organisations.
- • Explain how organisations are evolving their defenses in response.
2. Explore One Emerging Cybersecurity Trend (8 Marks)
- • Choose one trend such as predictive threat modelling using AI, cloud‑native security automation, or next‑generation encryption technologies.
- • Explain how this trend influences cybersecurity operations and discuss risks such as adversarial manipulation or misconfiguration.
Part B: Practical Cybersecurity Analysis: Threat Analysis and Mitigation
1. Hashing for Data Integrity (20 Marks)
- • Generate MD5, SHA‑256, and SHA‑3 hashes for a short message using a terminal‑based hashing program. Slightly modify the message and regenerate the hashes. Compare the outputs to demonstrate the avalanche effect.
- • Explain the importance of hashing for data integrity, password authentication systems, and digital signatures.
2. Open-Source Intelligence (OSINT) & Google Dorking for Security Analysis (8 Marks)
- • Conduct OSINT research using Google Dorking techniques. Provide examples of operators used, describe what can be exposed.
Provide screenshots of the hashing process and Google Dorking searches
References
Must consider at least six (6) current references from journal/conference papers and books. Must follow IEEE referencing style.
Assignment Instructions:
- • Do not use Wikipedia as a source or a reference.
- • Provide clear, labelled screenshots as evidence for practical exercises.